Welcome to Insanity – my fifth CTF. There is one flag on this CTF. Your objective is to gain root access.
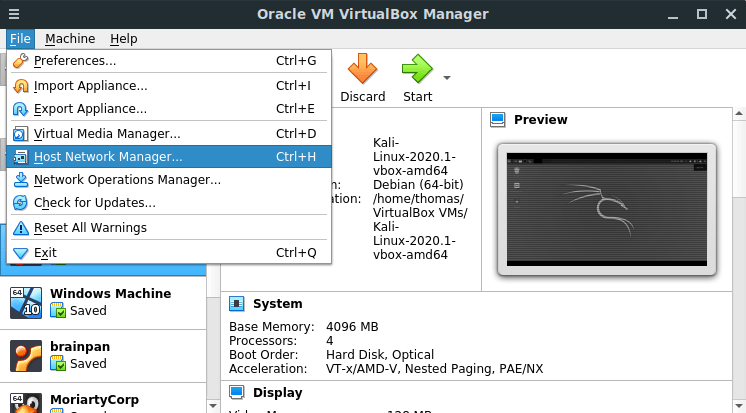
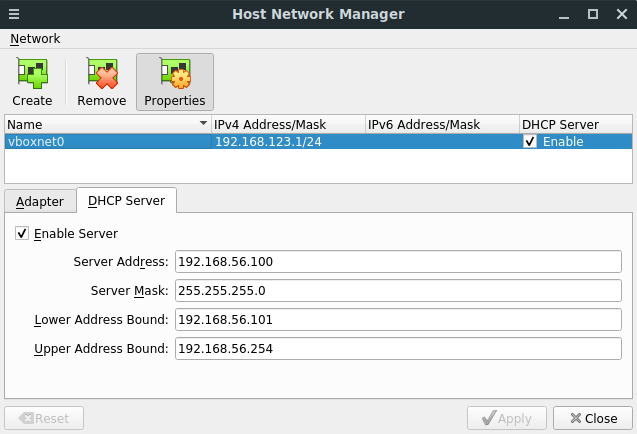
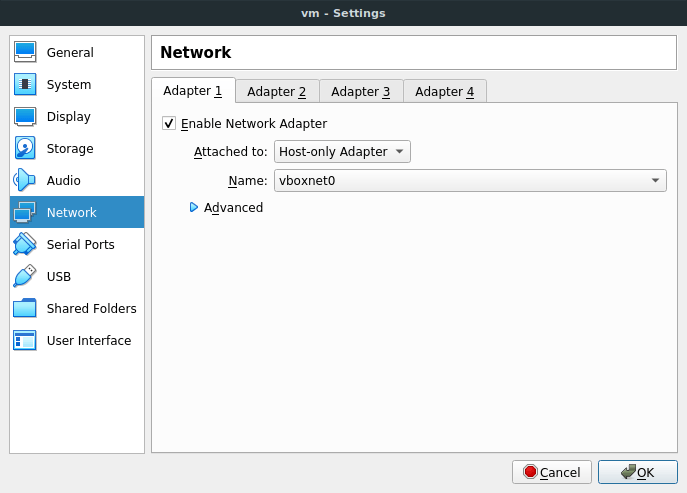
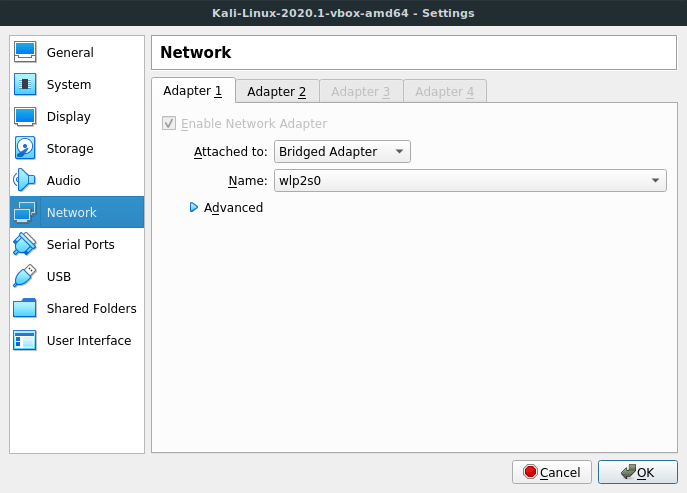
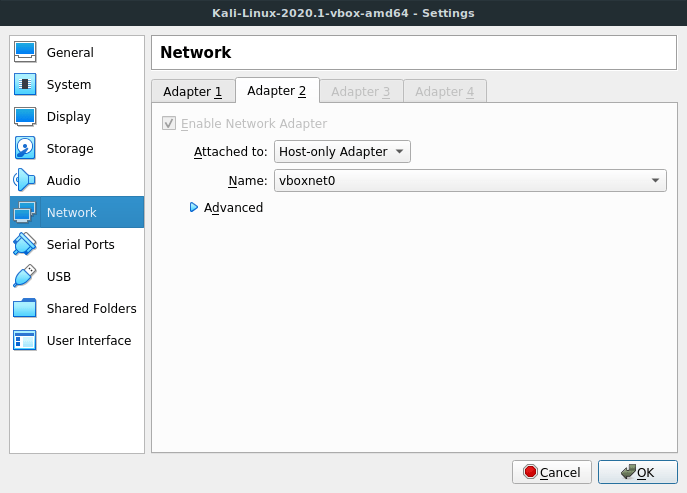
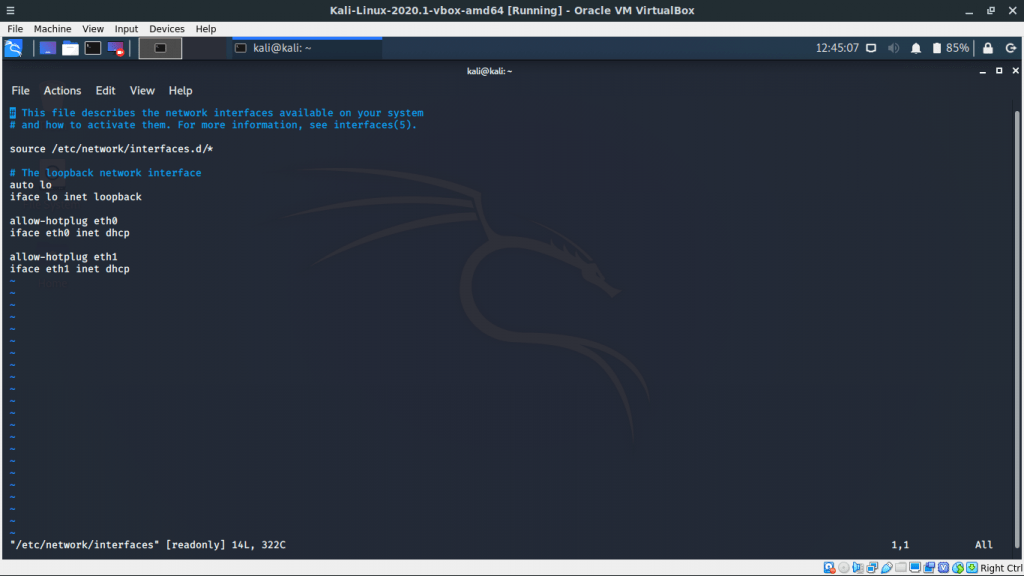
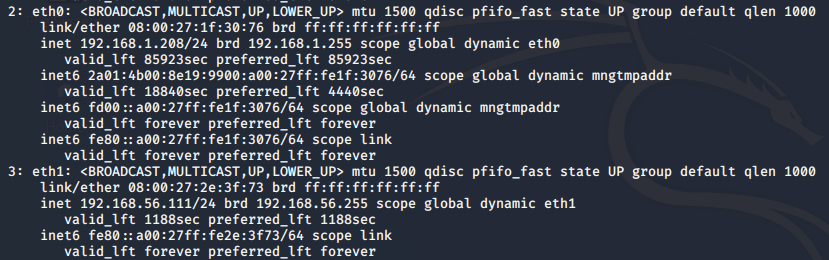
This CTF is rated as 5/5 for difficulty. What makes this CTF difficult is not necessarily the types of vulnerabilities you will find – instead, it’s the process of exploiting them. DHCP is enabled – this CTF has been tested on VirtualBox only, though I don’t think there’ll be issues if you run it with VMWare.
Synopsis
A web hosting provider has asked you to test their security. Can you find the vulnerabilities on their server and gain root access? If anyone wants to submit a written report for this, I’d give it a read and potentially publish it on this blog! 🙂
Note about hints
Please note, I will not be giving out hints for this CTF until at least the 30th August 2020. Try harder.
Edit: A few people have joined my Discord Server to share information (which is absolutely fine). Feel free to join and discuss ways to hack this CTF.
Download now
You can download Insanity here.
SHA-256: 75819bda88013d13465c9ec4145d56470378450e8c6c0c6faa8c72503a049850