This is my first Capture the Flag exercise and covers a number of different techniques.
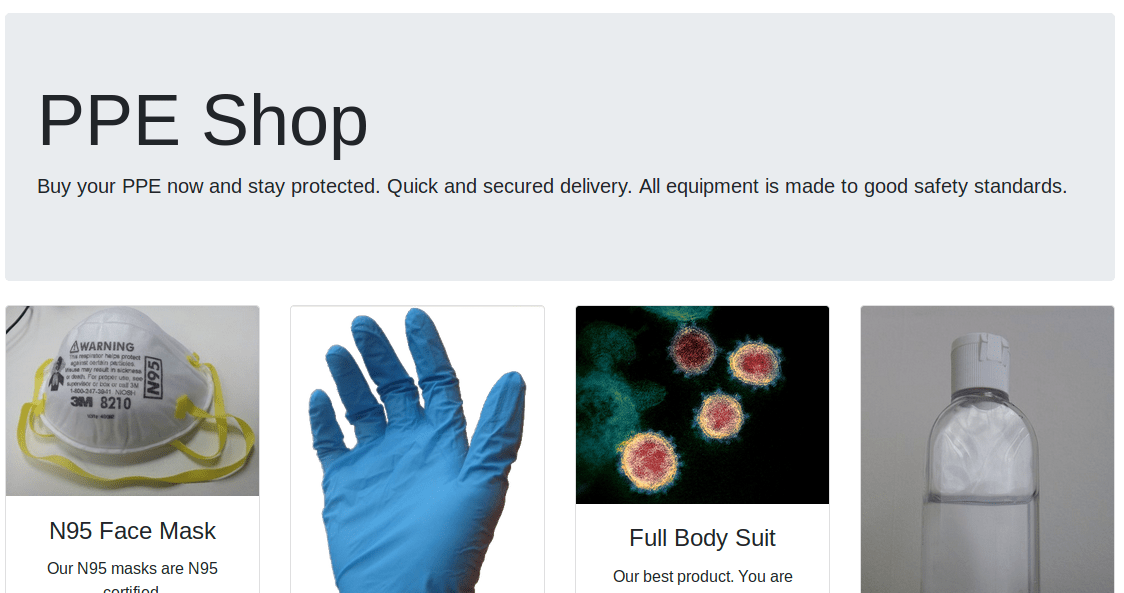
The back story: Scammers are taking advantage of people and various fake shopping websites have been setup, but people are finding their orders never arrive. We have identified one scam website which we believe is harvesting credit card details from victims. Your objective is to take down the scam website by gaining root access, and identify the 3 flags on their server. Our intelligence suggests the scammers are actively reviewing all orders to quickly make use of the credit card information.
The types of vulnerability used in this CTF can be seen below (they are intentionally hidden by default):
You can download the Capture the Flag here. This has been tested using VirtualBox but may work with other virtualisation platforms. DHCP is enabled, and it is recommended you run this in host-only network mode.
Please feel free to leave me feedback in the comments. I am keen to see what people thought about it and how easy/difficult they thought it was.
SHA-256: e840abca18c81bb269a02247a99416b0f63261f3a62d4b17b9436fb3387f70e7