Are they doing enough to protect victims? I don’t think they are.
I recently had a look at some of the Phishing websites I could find; mainly to see how these scammers are operating and what kind of Phishing campaigns they run.
It wasn’t too hard to find many Phishing websites by reviewing Twitter, Pastebin, and other sources. What did surprise me though is the sheer quantity of Phishing websites that are hosted by Namecheap. So much in fact that I believe Namecheap are largely responsible for a lot of the Phishing websites online. According to Petscams.com, 38% of scam domain names reported to them since 23rd August 2017 are sponsored by Namecheap. That’s insane! Their approach to dealing with these websites appears relaxed and under-resourced. Where they profit by selling these services, they have a responsibility to ensure they are not used inappropriately. I believe they are putting profit before this responsibility.
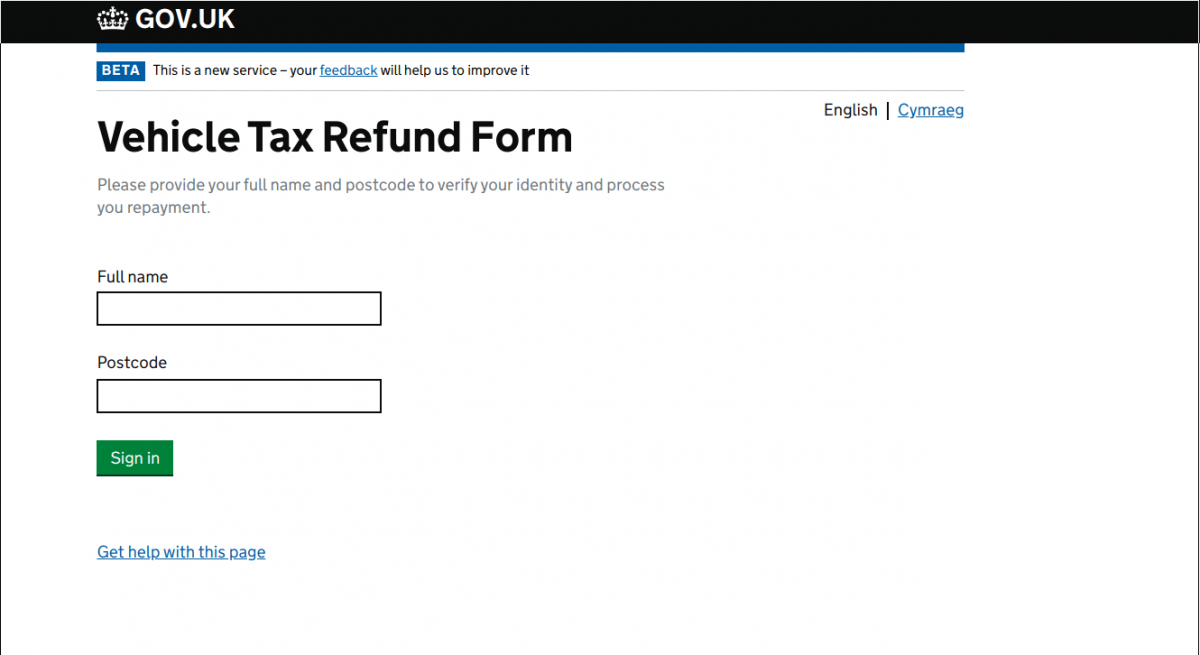
In my search for Phishing websites this morning, I identified the following URLs:
- hxxps://ee-securebilling.com/ (198.54.115.105)
- hxxps://netflixbilling-info.com/ (198.54.115.105)
- hxxps://dvla.gov.uk-rebate.ltd/ (68.65.122.147)
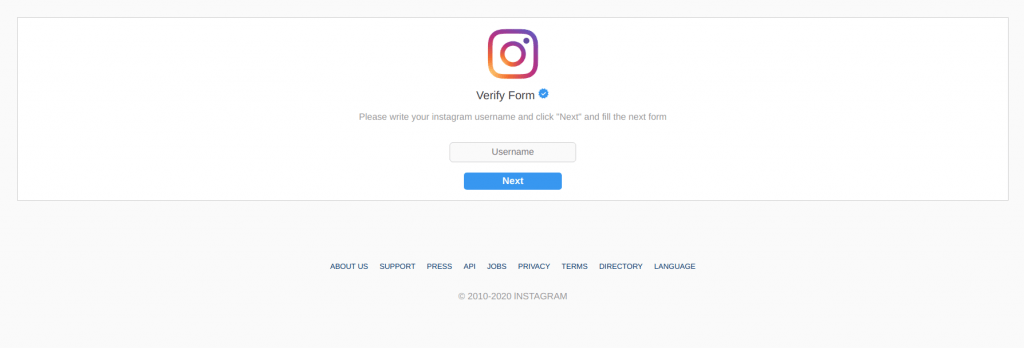
- hxxps://tickform-instagram.com/ (198.54.116.4)
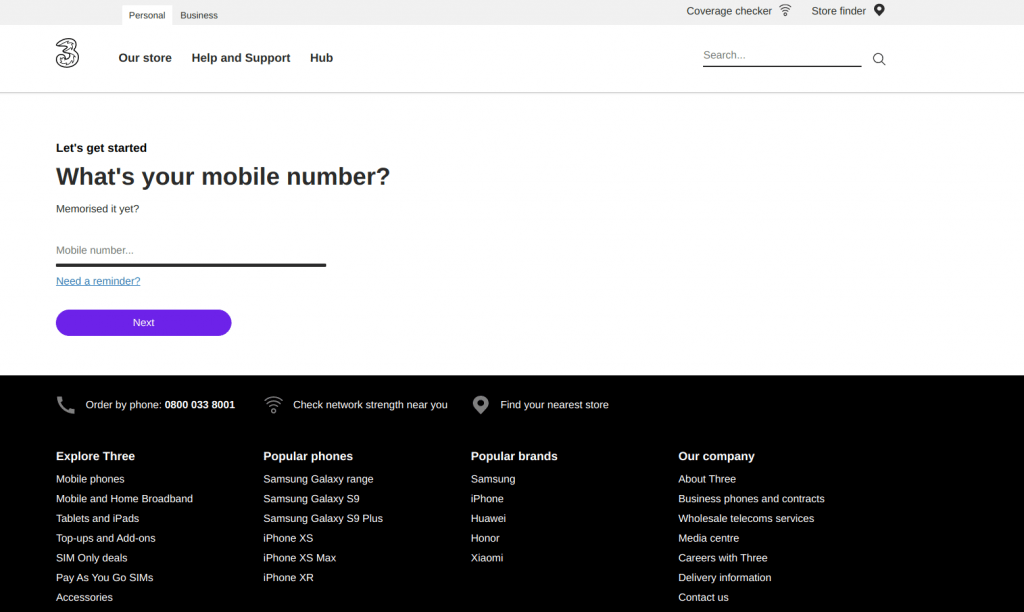
- hxxps://new-mythreepayment.com/ (198.54.116.224)
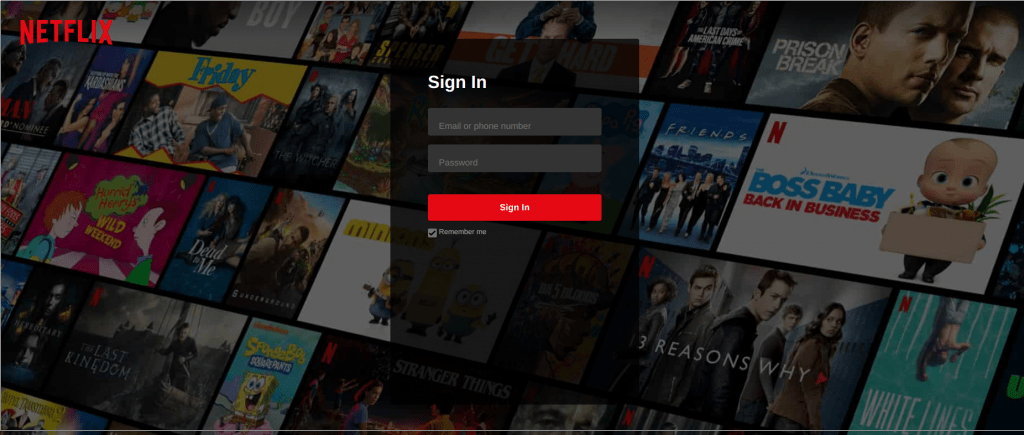
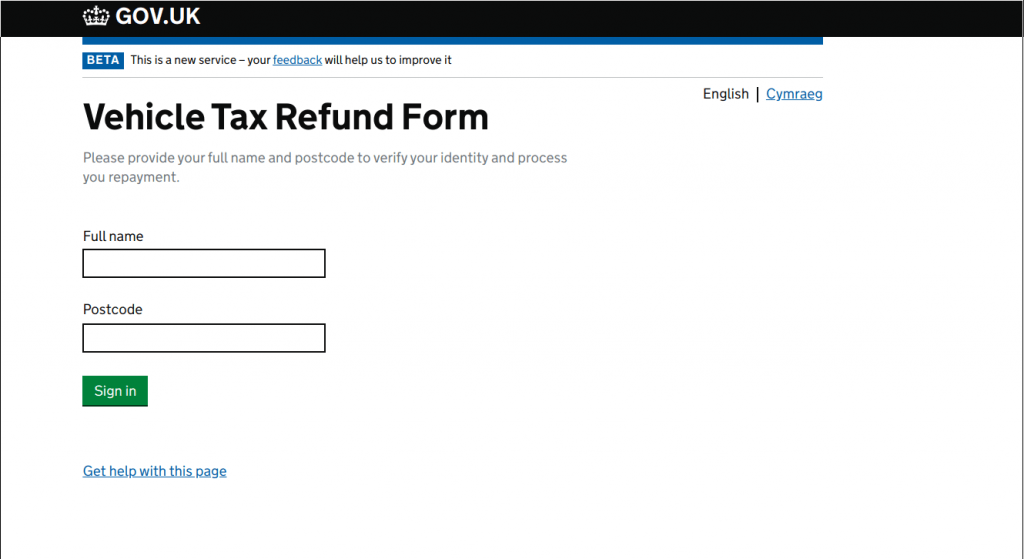
Every single one of these URL’s was/is hosted by Namecheap. Every new website I found continued with the same pattern. Namecheap Namecheap. Namecheap. Between them, they collected various bits of information from victims including dates of birth, credit card and bank details, e-mail addresses, and passwords.
Each of these URL’s were also reported to them between 9:00AM-11:10AM UK Time. A support representative replied to all tickets at 12:06PM advising they were investigating. At the time of writing this post, it is now 2:00PM and with the exception of the EE website which looks like it has been deleted by the phisher, all websites are still active actively phishing victims. I don’t feel it takes that much investigation from Namecheap for them to ascertain they’re not legitimate websites. I do not believe they are acting fast enough, and I think they have something to answer for. Real victims are being scammed. Real victims are losing their money. Namecheap do not seem to understand this.
Fraudsters are obviously using Namecheap’s services due to their relaxed approach at suspending them.
Interestingly enough, Facebook also litigated against Namecheap eariler this year.
The social networking giant claims that Namecheap has refused to cooperate in an investigation into a series of malicious domains that have been registered through its service and which impersonated the Facebook brand.
https://www.zdnet.com/article/facebook-sues-namecheap-to-unmask-hackers-who-registered-malicious-domains/
I have a few domain names registered with Namecheap, and whilst they probably make very little profit off of them, I cannot continue to support a company with such a relaxed approach to scams, and will be transferring them away shortly. I suggest you do the same.